This article is intended for system administrators who set security policy in enterprise environments that require smart card authentication.
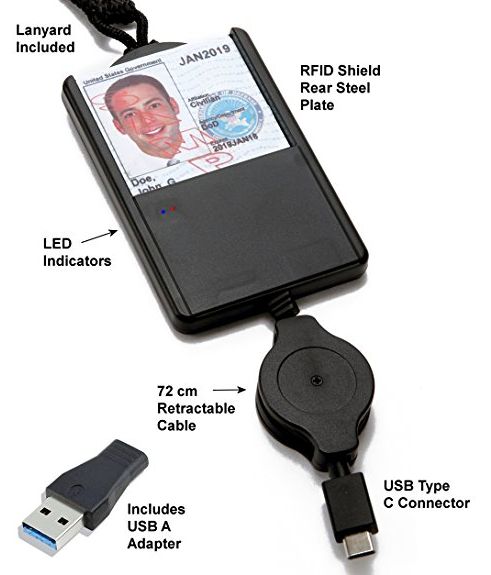
The package provides the installation files for SCM SCR3311 USB SmartCard Reader Driver version 4.58.0.0. If the driver is already installed on your system, updating (overwrite-installing) may fix various issues, add new functions, or just upgrade to the available version. Buy Type C Smart Card Reader Saicoo DOD Military USB-C Common Access CAC Card Reader, Compatible with Windows (32/64bit) XP/Vista/ 7/8/10, Mac OS X: Memory Card Readers - Amazon.com FREE DELIVERY possible on eligible purchases.
Enable smart card-only login
Make sure that you carefully follow these steps to ensure that users will be able to log in to the computer.
- Pair a smart card to an admin user account or configure Attribute Matching.
- If you’ve enabled strict certificate checks, install any root certificates or intermediates that are required.
- Confirm that you can log in to an administrator account using a smart card.
- Install a smart-card configuration profile that includes '<key>enforceSmartCard</key><true/>,' as shown in the smart card-only configuration profile below.
- Confirm that you can still log in using a smart card.
For more information about smart card payload settings, see the Apple Configuration Profile Reference.
For more information about using smart card services, see the macOS Deployment Guide or open Terminal and enter man SmartCardServices.
Disable smart card-only authentication
If you manually manage the profiles that are installed on the computer, you can remove the smart card-only profile in two ways. You can use the Profiles pane of System Preferences, or you can use the /usr/bin/profiles command-line tool. For more information, open Terminal and enter man profiles.
If your client computers are enrolled in Mobile Device Management (MDM), you can restore password-based authentication. To do this, remove the smart card configuration profile that enables the smart card-only restriction from the client computers.
To prevent users from being locked out of their account, remove the enforceSmartCard profile before you unpair a smart card or disable attribute matching. If a user is locked out of their account, remove the configuration profile to fix the issue.
If you apply the smart card-only policy before you enable smart card-only authentication, a user can get locked out of their computer. To fix this issue, remove the smart card-only policy:
- Turn on your Mac, then immediately press and hold Command-R to start up from macOS Recovery. Release the keys when you see the Apple logo, a spinning globe, or a prompt for a firmware password.
- Select Disk Utility from the Utilities window, then click Continue.
- From the Disk Utility sidebar, select the volume that you're using, then choose File > Mount from the menu bar. (If the volume is already mounted, this option is dimmed.) Then enter your administrator password when prompted.
- Quit Disk Utility.
- Choose Terminal from the Utilities menu in the menu bar.
- Delete the Configuration Profile Repository. To do this, open Terminal and enter the following commands.
In these commands, replace <volumename> with the name of the macOS volume where the profile settings were installed.rm /Volumes/<volumename>/var/db/ConfigurationProfiles/MDM_ComputerPrefs.plistrm /Volumes/<volumename>/var/db/ConfigurationProfiles/.profilesAreInstalledrm /Volumes/<volumename>/var/db/ConfigurationProfiles/Settings/.profilesAreInstalledrm /Volumes/<volumename>/var/db/ConfigurationProfiles/Store/ConfigProfiles.binaryrm /Volumes/<volumename>/var/db/ConfigurationProfiles/Setup/.profileSetupDone - When done, choose Apple () menu > Restart.
- Reinstall all the configuration profiles that existed before you enabled smart card-only authentication.
Configure Secure Shell Daemon (SSHD) to support smart card-only authentication
Users can use their smart card to authenticate over SSH to the local computer or to remote computers that are correctly configured. Follow these steps to configure SSHD on a computer so that it supports smart card authentication.
Update the /etc/ssh/sshd_config file:
- Use the following command to back up the sshd_config file:
sudo cp /etc/ssh/sshd_config /etc/ssh/sshd_config_backup_`date '+%Y-%m-%d_%H:%M'` - In the sshd_config file, change '#ChallengeResponseAuthentication yes' to 'ChallengeResponseAuthentication no' and change '#PasswordAuthentication yes' to '#PasswordAuthentication no.'
Then, use the following commands to restart SSHD:
sudo launchctl stop com.openssh.sshd
sudo launchctl start com.openssh.sshd
If a user wants to authenticate SSH sessions using a smart card, have them follow these steps:
- Use the following command to export the public key from their smart card:
ssh-keygen -D /usr/lib/ssh-keychain.dylib - Add the public key from the previous step to the ~/.ssh/authorized_keys file on the target computer.
- Use the following command to back up the ssh_config file:
sudo cp /etc/ssh/ssh_config /etc/ssh/ssh_config_backup_`date '+%Y-%m-%d_%H:%M'` - In the/etc/ssh/ssh_config file, add the line 'PKCS11Provider=/usr/lib/ssh-keychain.dylib.'
If the user wants to, they can also use the following command to add the private key to their ssh-agent:
ssh-add -s /usr/lib/ssh-keychain.dylib
Enable smart card-only for the SUDO command
Use the following command to back up the /etc/pam.d/sudo file:
sudo cp /etc/pam.d/sudo /etc/pam.d/sudo_backup_`date '+%Y-%m-%d_%H:%M'`
Then, replace all of the contents of the /etc/pam.d/sudo file with the following text:
Enable smart card-only for the LOGIN command
Use the following command to back up the /etc/pam.d/login file:
sudo cp /etc/pam.d/login /etc/pam.d/login_backup_`date '+%Y-%m-%d_%H:%M'`
Then, replace all of the contents of the/etc/pam.d/login file with the following text:
Enable smart card-only for the SU command
Use the following command to back up the /etc/pam.d/su file:
sudo cp /etc/pam.d/su /etc/pam.d/su_backup_`date '+%Y-%m-%d_%H:%M'`
Then, replace all of the contents of the/etc/pam.d/su file with the following text:
Sample smart card-only configuration profile
Here’s a sample smart card-only configuration profile. You can use it to see the kinds of keys and strings that this type of profile includes.
Here are the steps on how to install a CAC Reader for Mac:- Ensure your CAC reader works with Mac
- Check to ensure your Mac accepts the reader
- Check your Mac OS version
- Check your CAC’s version
- Update your DOD certificates
- Guidance for Firefox Users
- Look at graphs to see which CAC enabler to use
Step 1: Purchase a Mac Friendly CAC Reader
Purchase a CAC reader that works for your Mac. There are only a couple that you can choose from and I’ve listed them below.
If you already have a CAC reader and it isn’t Mac friendly, you could update the firmware, however, for the non-tech savvy people out there, it’s probably better to just purchase a new one and save the headache – they’re only ~$11-13 dollars.
Best Mac Compatible CAC USB Readers
Best Mac Compatible CAC Desk Readers
Step 2: Plug in and Ensure It’s Accepted
Once you have your CAC reader, plug it into your Mac and ensure your computer recognizes it. If you have one of the CAC readers we suggested above, then you should be good to go.
If for some reason your CAC reader isn’t working, you may need to download the appropriate drivers for your CAC reader. You can find these drivers on the Reader’s Manufacturer Website.
Step 3: Update Your DOD Certificates
Now that you have your CAC reader connected and accepted on your Mac computer, it’s time to ensure you have the right certificates in order to access DOD CAC required web pages.

Procedure for Chrome and Safari
- Type ⇧⌘U (Shift + Command + U) to access your Utilities
- Find and Double click “Keychain Access”
- Select “Login” and “All Items”
- Download the following five files and double click each once downloaded so as to install in your Keychain Access.
- When you double-click the Mac Root Cert 3 and 4, you’ll need to tell your browser to always trust them. Click the button like you see below:
Additional Steps for Firefox
If you’re using Mozilla Firefox as your primary browser, you’re going to need to perform some additional steps. First, perform the same steps that you did for Chrome and Safari. Afterwards, follow these additional steps to get started.
- Download All Certs zip and double click to unzip all 39 files
- While in Firefox, click “Firefox” on the top left, then “Preferences”
- Then Click “Advanced” > “Certificates” > “View Certificates”
- Then Click “Authorities” and then “Import”
- Import each file individually from the “AllCerts” folder. When you do this, the below box will popup. Check all three boxes and click “OK”
Step 4: Download and install CAC Enabler
Choosing the right CAC enabler can be pretty tricky. It all depends on what OS you have installed, how you installed it, and even what kind of CAC Card you have!
Usb Smart Card Reader Drivers
In order to get the right enabler, be sure to visit our trusty guide to Mac CAC Enablers! It’ll walk you through exactly which enabler is right for you.
CAC Access at Home Success
Now that you have a CAC reader, certificates, and a CAC Enabler, you should now be able to access any CAC-enabled website and log on using your CAC password and data.
Scr3311 Smart Card Reader Drivers For Mac Download
Common Reasons Why Your CAC Card Won’t Work On Your Mac
Ensure Your CAC Card Meets the Standards: In order for your CAC card to work, it must meet the minimal requirements. Currently, there are only four types of CAC cards that can be used. The ensure you have the right CAC card for online access, flip your CAC card to the back and if you have one of the below numbers written on the top left, then you are good to go:
- G&D FIPS 201 SCE 3.2
- Oberthur ID one 128 v5.5 Dual
- GEMALTO DLGX4-A 144
- GEMALTO TOP DL GX4 144
Scr331 Driver
If you do not have any of the above written on the back, then proceed to your nearest PSD to get a new CAC card issued.